Poste Italiane phishing emails
Poste italiane is the government-owned postal service of Italy and spammers use phishing techniques to trick people to send their credentials of online accounts and credit cards.
The first of april i received an email from bancoposta@bpolbpol.com with this content.
Basically it says that i have been selected to get a bonus of 250 euro and in order to complete the operation i must download the attachment.
First of all we see that the domain of the sender is neither poste.it or postepay.it, this is kinda strange to be a legitimate email. I was curious to know the type of site behind the domain so i navigate to that url and i get a white screen with a blue write "website under construction".
Maybe we can get more information checking throgh http://whois.domaintools.com who registered that domain.
Few details:
The strange think about this website is that it has never been linked or added to google, so no one can find it throught a search engine. Since it's not linked i cannot search for a chaced page, consequently i cannot know what type of website was running.
We take a brief look to nslookup and we discover that has its own mail server.
Since we cannot know if this site was operable i can say that the smtp server was used to spread spam without the owner's knowledge.
Now it's time to see what is the attachment. It's a simple html file called Document.html and if you open with a browser you get a postepay page with a central form where are listed different fields such as username, password, credit card number, expiration date and security code ready to be filled.
As you can see it looks very similar to the original, they did a pretty good job.
One thing to notice is the year of expiration date that still use 2011, this mean that the html page was created the past year and they haven't updated yet.
Where are sent this information ?
To find out we open our fake page with an editor like notepad++ and there are two lines, one regarding the copyright and the other one is kinda funny because tell you that the source code is not available.
If you scroll down you see at the end of the page there are few lines of html with obfuscated javascript
The code has been converted from ASCII to hexadecimal and to reverse the process it uses a javascript function called unescape.
Once decoded the most important thing to do was to find the "collector site" that must be the value of the action attribute of form tag.
The downloaded page will perform a POST request to gogeamitu.com/soso/system.php with all the sensitive information. This php script can act in several ways, but what i think is it can do one of this things:
To know if this site has been compromised or is the server of the spammer we take a look to the domain through a whois service (like the previous).
Domain details:
I found the cached page only on google and was taken the 28 of march, this is too far from the register date to say that has never been chaged. Another interesting thing is the domain name gogeamitu which is the name of an old Romanian boxer Gogea Mitu, maybe this is a clue about spammers nationality ?
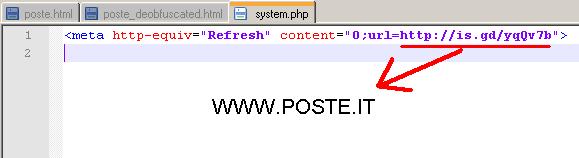
Visible content of system.php is down here and it is composed by only one line that redirect the victim to poste.it.
In my opinion spammers have payed one person to use his personal information to register gogeamitu and store (*) in this server all victims details, maybe once a day they retrieve the data and clean the db.
* After doing other reasearch on others phishing emails he (i'm quite sure is only one person) doesn't store the information to the db, but send an email to his personal address.
The first of april i received an email from bancoposta@bpolbpol.com with this content.
Basically it says that i have been selected to get a bonus of 250 euro and in order to complete the operation i must download the attachment.
First of all we see that the domain of the sender is neither poste.it or postepay.it, this is kinda strange to be a legitimate email. I was curious to know the type of site behind the domain so i navigate to that url and i get a white screen with a blue write "website under construction".
Maybe we can get more information checking throgh http://whois.domaintools.com who registered that domain.
Few details:
- Record created: 2/7/2011
- Record expires: 2/7/2012.
- Registration service provider: Aruba S.p.A.
The strange think about this website is that it has never been linked or added to google, so no one can find it throught a search engine. Since it's not linked i cannot search for a chaced page, consequently i cannot know what type of website was running.
We take a brief look to nslookup and we discover that has its own mail server.
Since we cannot know if this site was operable i can say that the smtp server was used to spread spam without the owner's knowledge.
Now it's time to see what is the attachment. It's a simple html file called Document.html and if you open with a browser you get a postepay page with a central form where are listed different fields such as username, password, credit card number, expiration date and security code ready to be filled.
One thing to notice is the year of expiration date that still use 2011, this mean that the html page was created the past year and they haven't updated yet.
Where are sent this information ?
To find out we open our fake page with an editor like notepad++ and there are two lines, one regarding the copyright and the other one is kinda funny because tell you that the source code is not available.
If you scroll down you see at the end of the page there are few lines of html with obfuscated javascript
The code has been converted from ASCII to hexadecimal and to reverse the process it uses a javascript function called unescape.
Once decoded the most important thing to do was to find the "collector site" that must be the value of the action attribute of form tag.
The downloaded page will perform a POST request to gogeamitu.com/soso/system.php with all the sensitive information. This php script can act in several ways, but what i think is it can do one of this things:
- Stores the information in the database of the same server
- Send the information to a remote database or to another web page
- Send an email to spammers with all information
To know if this site has been compromised or is the server of the spammer we take a look to the domain through a whois service (like the previous).
Domain details:
- Record created 21 February 2012
- Record expire 21 February 2013
- Registration service provider: Aruba S.p.A.
Again some details are omitted and also in this case the owner details are fully visible. This domain has been registered only one month ago but this time is linked so i can check the webchace of various search engines.
Current home page.
Current home page.
I found the cached page only on google and was taken the 28 of march, this is too far from the register date to say that has never been chaged. Another interesting thing is the domain name gogeamitu which is the name of an old Romanian boxer Gogea Mitu, maybe this is a clue about spammers nationality ?
Visible content of system.php is down here and it is composed by only one line that redirect the victim to poste.it.
In my opinion spammers have payed one person to use his personal information to register gogeamitu and store (*) in this server all victims details, maybe once a day they retrieve the data and clean the db.
* After doing other reasearch on others phishing emails he (i'm quite sure is only one person) doesn't store the information to the db, but send an email to his personal address.












Comments
Post a Comment